The ONL Tutorial
Filtering With TCP Flags
There are six TCP flag bits in the TCP header which can be used
to identify packets that have any of these bits ON:
- A connection is starting (SYN).
- A connection is ending (FIN).
- A connection is being reset (RST).
- The packet is an acknowledgement (ACK).
- Pass all outstanding packets at the receiver to the
application as soon as possible (PSH).
- There is urgent data in the packet (URG).
For example, we count the number of TCP connection attempts by
matching all TCP packets with the SYN bit on if we know the
sender's IP address.
Or, we can simulate a SYN flood attack by dropping all TCP packets
from a sender except for its SYN packet.
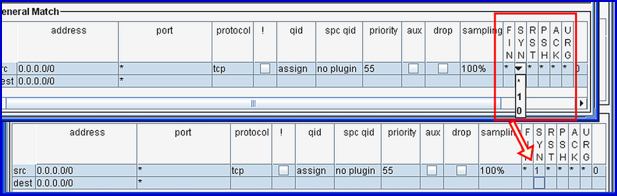
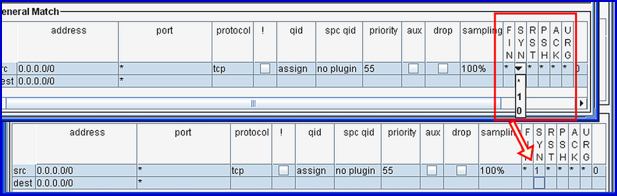
Fig. 1. TCP Flags Field in a GM Filter.
You can filter on the TCP flag fields (SYN, ACK, FIN, RST, PSH, URG)
using a GM (General Match) filter (Fig. 1).
Fig. 1 shows an egress GM filter that could be used to count TCP connection
attempts; i.e., it will match a TCP SYN packet coming from anywhere and
going anywhere and forward it in the usual manner.
The main things to remember are:
- The TCP flag fields can have only one of three values:
* (don't care), 0, or 1.
- The only time a TCP flag field can be a value other than
don't care (*) is if the protocol field is tcp.
- A packet matches a GM filter if it matches the 5-tuple portion
of the filter (src address, src port, dst address, dst port, protocol)
and all of the TCP flag fields.
- An auxilliary filter can not drop packets.
The Using TCP Flags
example demonstrates how to use the TCP-flags feature to:
- Count TCP connection attempts
- Count TCP flow completions
- Simulate a SYN flood attack
A new version of the
SYN Attack Mitigation Demo will also demonstrate how TCP flag
filtering can be used.
Revised: Mon, Jan 28, 2008